Before you reach out to vendors, it’s important to know exactly what you want from them. What are your company’s business objectives? What are your needs? In this article, you’ll discover exactly how to identify these important facets of your business so that you can get the most out of the telecom procurement process.
Need some assistance identifying your business objectives and needs? Get in touch with Technology Procurement Group, where we have the industry expertise and experience to guide you through the telecom or IT procurement process. Just fill out the form on our Contact Us page for more information, or reach out by phone at 1-888-449-1580 or email at info@TPG-llc.com.
Contents
Evaluate Your Company’s Current Telecom Provider
After your company has prepared for the telecom procurement process, it’s time to evaluate its current telecommunications provider.
This allows your procurement team to identify the areas in which its current provider is doing well, as well as where it comes up short.
Procurement professionals can then determine the business’s particular telecom needs and figure out exactly what they need and expect from a telecommunications provider.
Several facets and contributing factors should play a part in your company’s evaluation of its current provider. This evaluation mainly consists of answering various questions about the provider, the products and services it offers, and how well it functions.
Current Products and Services

The first step is for your procurement team to list all of the telecom products and services that the company is currently using and answer the following questions about them.
- Are the products and services meeting the company’s expectations and working in the way they’re intended to? (For example: Are the company’s WAN, SD-WAN, and internet connections fast enough? Does the business experience frequent outages, and what are the business impacts of network downtime?)
- Are there any products or services the business’s current telecom provider does not offer that you’d like to have in the future?
Pricing
Next, your company’s procurement professionals must consider the amount the company is currently paying for telecommunications products and services.
- Does the pricing fit the company’s budget?
- Is the company being overcharged or falling prey to hidden fees that are driving up the bottom line?
- Is the current provider’s pricing transparent and accurate to the contract terms?
- Is the company paying a fair price for the products and services it is using?
- Is there an opportunity to reduce the number of vendors and complexity of telecom contracts to leverage additional cost savings?
Customer Service and Support

Excellent customer service and support are must-haves when working with a telecom provider.
- Is the company constantly switched from rep to rep?
- Is the provider familiar with the company’s history and telecom needs?
- When contacting the telecom provider, is the company stuck speaking with a bot or automated system, rather than connecting with a real person?
- Are telecom issues generally resolved with a single call, or does it take multiple attempts to adequately address a problem?
- What is the provider’s support history? Does it act as a partner, rather than just a vendor?
- Is the provider proactive or reactive?
Flexibility and Scalability
Flexibility and scalability are key, especially for growing and expanding businesses.
- Does the current telecom provider have the capacity and resources to grow with the company?
- Is the current provider flexible in adjusting the company’s products and services as its needs change?
- Is the provider forward-looking? Does it aggressively move to new, updated technologies?
- Does the current carrier focus on automation and other tools to help the company better manage its network and order new services?
Security and Reliability
Two more necessary qualities in a telecom provider are security and reliability, and these have grown to be increasingly important as of late. Data breach numbers, costs, and impacts all rose in 2021. According to one report from IBM and the Ponemon Institute, the average cost of a data breach increased to $4.24 million in 2021, the highest figure in 17 years. In addition, the number of data breaches through September of 2021 surpassed 2020’s numbers by a whopping 17%.
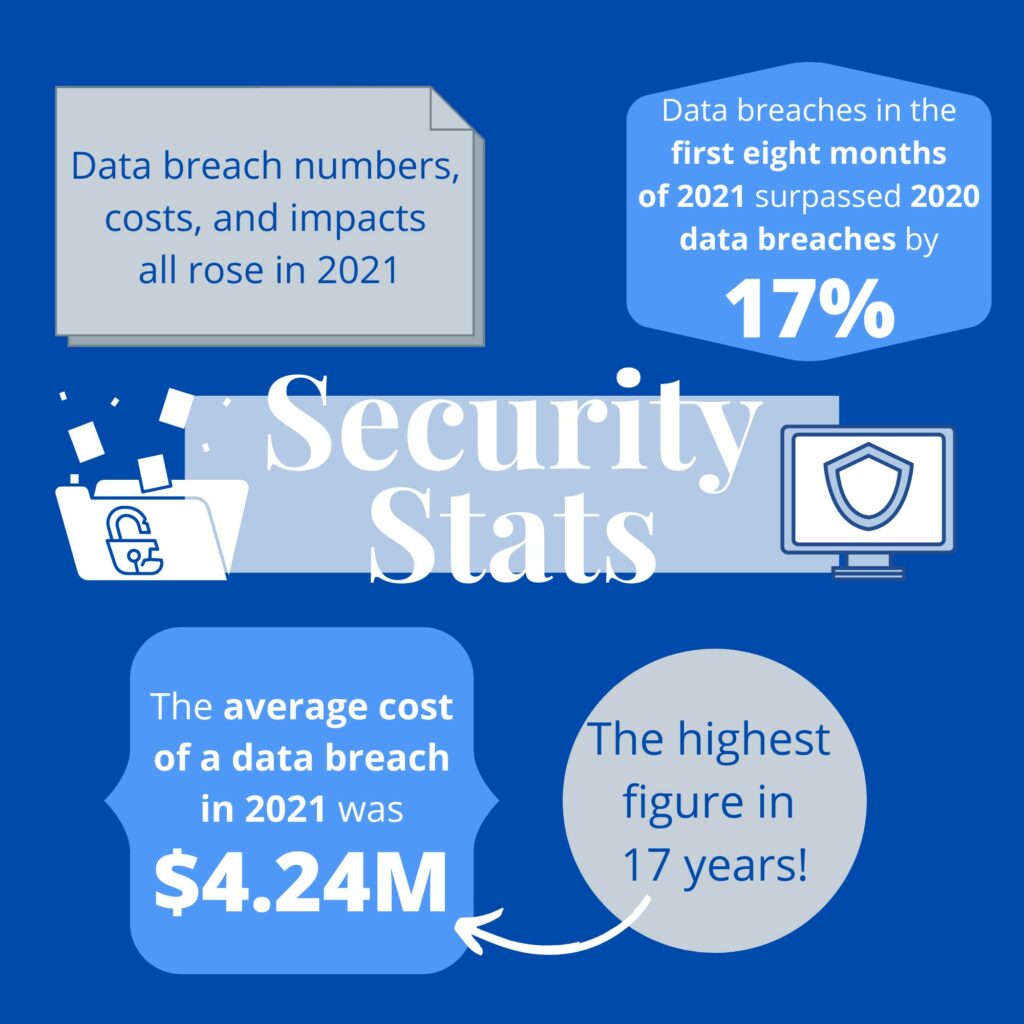
The impact of remote work due to the coronavirus pandemic has played a role in this increase, which is an important factor for enterprises to consider.
It’s more crucial than ever for companies to take notice of data breaches and other security issues; the security and reliability of the current telecom provider and all potential vendors should play a notable role in the procurement process.
When considering the security and reliability of the business’s current provider, the procurement team must look at its relationship with the provider over the length of the contract.
- Have there ever been issues with data breaches?
- Is the company’s connection consistent, or does it go down frequently?
- How quickly are outages resolved?
- Has the current telecom company been around for a long time and proven that it’s reliable, or is it a newer company that may not be around for the foreseeable future?
Transparency
Transparency is crucial for companies to have a positive relationship with their telecommunications providers. Transparency is especially vital when it comes to communication and billing.
- Does the company find it simple and efficient to contact the carrier as needed?
- Is the company’s rep straightforward and clear in their responses, or do they use technical jargon and confusing verbiage to obscure the true meaning of what they’re saying? It is also necessary to understand common telecom acronyms and their meanings to understand IT procurement objectives.
- Have the enterprise’s account rep and support team changed during the contract term? If so, what was the impact?
- Is it clear what the company is being charged for as far as billing?
- Does the company ever encounter confusing phrases in bills that make it wonder if it’s paying unnecessary fees that weren’t a part of the initial agreement?
Overall Satisfaction

It may help to assign your company’s level of satisfaction a number between one and ten to make it more of an objective measure.
- How does the company feel about its current provider in general?
- Is the company satisfied, or did the current provider fail to meet its expectations?
- Does the provider offer formal opportunities for feedback, such as quarterly service reviews?
What the Company Likes and Dislikes
The final factor for your company to consider when evaluating its current telecom provider is its overall pros and cons.
- What does the company like about the provider?
- What does the current telecom provider do well?
- Where could the current provider improve to better serve the company?
- If the company were to renew its contract, what would need to change, or what would it need to see from its current telecom provider?
Identify Your Business’s Telecommunications Needs

Your business has already identified many of its telecommunications needs through the process of evaluating its current telecom provider.
The following questions will allow your company’s procurement team to further narrow down these needs and produce concrete statements that clearly state what the company requires from a telecom provider.
Specific Products, Services, and Features
- Considering the products and services the company is using now, which of them are necessities?
- Are there any products or services that the company’s current telecom provider does not offer, but that it needs or wants to add to its contract?
Below, find additional information regarding various services the company may wish to consider.
Consider Hyperautomation and Its Role in Telecom Procurement and IT Operations
Should the organization look for a vendor that offers hyperautomation technology? While the term “hyperautomation” may sound intimidating, it’s simpler than it seems.
Basically, hyperautomation takes automation to another level by fully automating as many once-manual tasks as possible. Gartner named it one of the top tech trends in 2021, claiming that it was the key to operational resiliency and digital operational excellence for organizations.
According to Gartner, “Hyperautomation is irreversible and inevitable. Everything that can and should be automated will be automated.” It also predicted that hyperautomation would reduce managers’ workloads by as much as 69% by 2024.
Hyperautomation combines multiple advanced technologies to automate any and every task that can be automated. This could include number-crunching, going through job applications, sending out paperwork and forms, and so much more.
Typically, the technologies used for hyperautomation include artificial intelligence (AI), machine learning (ML), and robotic process automation (RPA). Combining these technologies streamlines all repetitive business processes so that they no longer require manual intervention.
As one can imagine, implementing hyperautomation can significantly affect an organization, enabling it to better contend with competitors while gaining cost and resource efficiencies. Hyperautomation helps businesses get ahead in today’s resource-starved, highly distributed, fast-paced environment. It’s especially helpful for companies operating remotely since there are so few employees working in person at their facilities.
Who Needs Hyperautomation?

Every company can benefit from hyperautomation. It doesn’t matter whether your business’s processes are already automated or not, and it doesn’t make a difference whether your equipment is old or new.
Hyperautomation is excellent for organizations that feel the need to keep up with demand or who are using outdated work processes that make it difficult to compete.
It’s also beneficial for businesses whose corporate IT employees cannot keep up with the company’s needs due to a lack of resources and knowledge. Employee ambition, curiosity, and a desire for high-quality products with consistent production and reduced human error are also reasons to adopt hyperautomation. Organizations that are struggling to meet regulatory compliance can benefit from it as well.
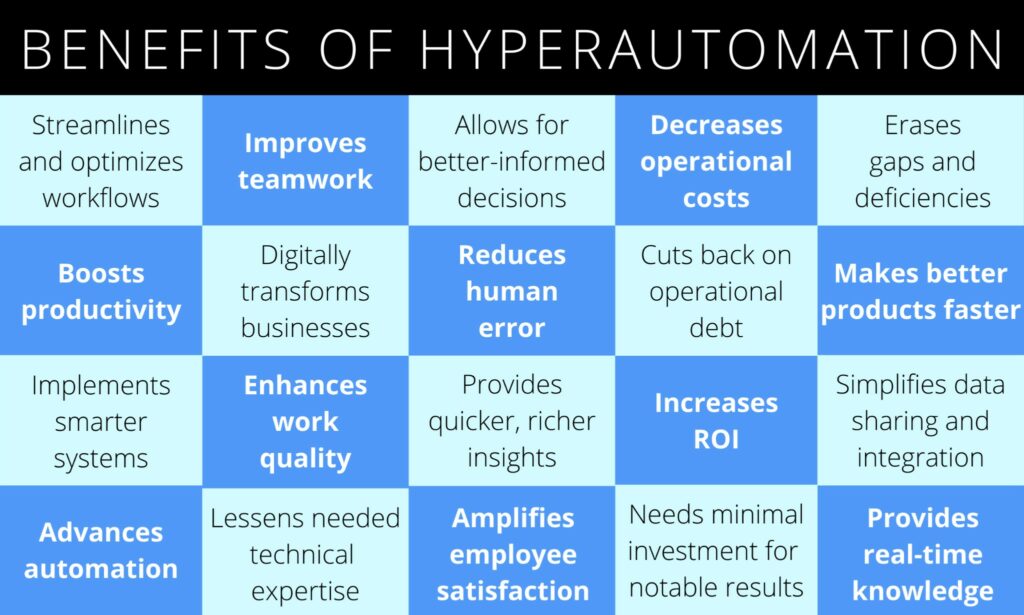
Benefits of Hyperautomation
There are dozens of advantages of implementing hyperautomation. Here are several:
Challenges of Hyperautomation
As with any new form of technology, some challenges come with advancement. One common challenge is knowing how to measure procurement performance with hyperautomation. Another is developing and sticking to a realistic project timeline.
Ensuring that the organization has end-to-end leadership for the entire project can also be a challenge, along with calculating ROI, both tangible and intangible, upfront and as accurately as possible.
Yet another challenge is choosing from the vast and evolving roster of products to select the ideal solution for the company. Finally, gaining management and stakeholder support for this new and unfamiliar approach can also be challenging.
Tips for Hyperautomation Implementation
When unsure how to begin with hyperautomation, the best move is to work with an expert who can assess the company’s needs and select the right tools for the project. There are many AI, ML, and RPA businesses that can help.
Using effective change management strategies and techniques will also prove helpful, as implementing new technology is always an adjustment for employees and the organization as a whole.
Relying on internal expertise by identifying the business’s current process experts from the technical and the business side will be beneficial. These individuals should be involved in the hyperautomation project from the beginning.
Adopting a proactive, top-down approach to building support and enthusiasm is also effective. Ensuring buy-in from customers, stakeholders, and management will provide exponential returns.
However, some employees are likely to fear replacement because hyperautomation takes over many of the tasks they are currently responsible for. It’s important to assuage their fears and keep them informed about how they’ll be affected by this new technology.
Whenever possible, provide comprehensive training for employees to create a more knowledgeable user base as well as to ease concerns about job security and longevity. Often, with training comes increased support and faster resolution of any issues that arise, since many employees will have the knowledge to troubleshoot problems with the new technology.
It’s also helpful for employees if they can explore the new technology risk-free. This helps them develop a higher comfort level and more familiarity with hyperautomation. It also aids the organization in determining where extra training and assistance may be necessary.
Be sure to identify any risks or barriers to implementing hyperautomation and mitigate them upfront. This will help the process move smoothly and stay on schedule.
Process mining can help evaluate the company’s existing processes to determine which should be hyperautomated first and which can wait.
Hyperautomation in IT Operations
In IT operations, there are plenty of processes that can be hyperautomated, from discovery and user provisioning to patch management, incident management, and change management. Currently, there is no off-the-shelf IT hyperautomation platform, but using a combination of AI, ML, and RPA provides a solid foundation.
Hyperautomation can also be used for auto-discovery and dependency mapping in order to keep track of complex IT infrastructures, assets, and configurations. Another application is AIOps, which aggregates operational data from monitoring tools and log files. With hyperautomation, AIOps solutions can centralize data and use ML to correlate alerts from various systems into a time-sequenced incident.
5 Areas for Hyperautomation in IT Operations
Automate routine housekeeping and operational tasks with RPA attended or unattended workflows.
- Use AI to automatically correlate alerts at scale and immediately identify root causes.
- Combine machine learning with decision tables to develop automated first response access to run auto-remediation workflows or suppress alerts.
- Utilize AI/ML-driven data analysis to identify and report alert patterns to predict and prevent incidents. Further integrate this with RPA workflows to take preventive actions before customers and users are affected.
- Use NLP (Natural Language Processing) to enrich log events and understand their meaning.
A Note on Digitizing Operations

When digitizing operations, ROI and culture should be the primary concerns. Anytime a company converts its non-digital operations to a digital platform, there are many shifts and changes, but keeping a focus on culture and ROI can help digitization go successfully.
ROI
Digitizing operations requires an investment; according to the International Data Corporation, organizations are projected to spend nearly $2 trillion on digital transformation in 2022. How can the organization best ensure a good ROI? Well, deciding exactly how to measure ROI is advantageous; many companies fail to establish metrics that will help them effectively evaluate their return on investment.
Start by identifying the project, reviewing business goals, determining investment and value metrics, and setting a timeframe. This structures the project to be easily measurable in terms of ROI.
A few additional tips include:
- Building the organization’s ROI model ahead of time
- Communicating pertinent information to all employees involved or affected
- Evaluating technology options carefully, since the company’s choice of technology can have a significant impact on ROI
Culture
How does digitizing operations affect the company culture? There are many ways; for example, companies become more proactive rather than reactive due to digitization.
Businesses also become more customer-centric, and data becomes more future-focused. Failure is expected and even embraced, and there is more of a flat organization with cross-functional teams than a siloed hierarchy.
Company culture comprises vision and strategy, leadership and people, and processes and organizational structure.
The key is to weave the eight dimensions of digital culture into these three company culture categories. The eight dimensions are:
- Digital leadership
- Digital technology and processes
- Autonomous working conditions
- Agility
- Entrepreneurship
- Collaboration
- Innovation and learning
- Customer orientation

Incorporating the eight dimensions with the three parts of company culture ensures more success with digitization. Meanwhile, the biggest threats to a thriving digital culture include a silo mindset, fear-of-failure perspective, and weak customer focus.
Putting effort into engagement and connection between departments can prevent the silo mindset, and accepting failure as a part of growth can help with the fear-of-failure perspective. Shifting the company’s focus from its products and services to its customers takes care of the final threat of weak customer focus.

Of course, clear and transparent communication and efforts to educate all employees regarding the changes to come are also crucial. Effective change management strategies are beneficial when implementing new technology.
Data Center Colocation Service Details

Many organizations utilize data center colocation services, or the storage of the company’s privately-owned servers and networking equipment in a third-party data center. This is the opposite of the in-house scenario, in which the company’s servers are housed within its own infrastructure. With data center colocation, the company rents space in a colocation data center or third-party data center.
Colocation centers are shared facilities in which the companies housing their equipment share costs, making the service cheaper than building a new data center. It’s ideal for enterprises that require full control over their equipment, and it can provide access to higher bandwidth levels. In general, colocation centers are highly reliable and offer high levels of physical protection.
Still, even with all the benefits of utilizing data center colocation services, there are a few considerations to keep in mind.
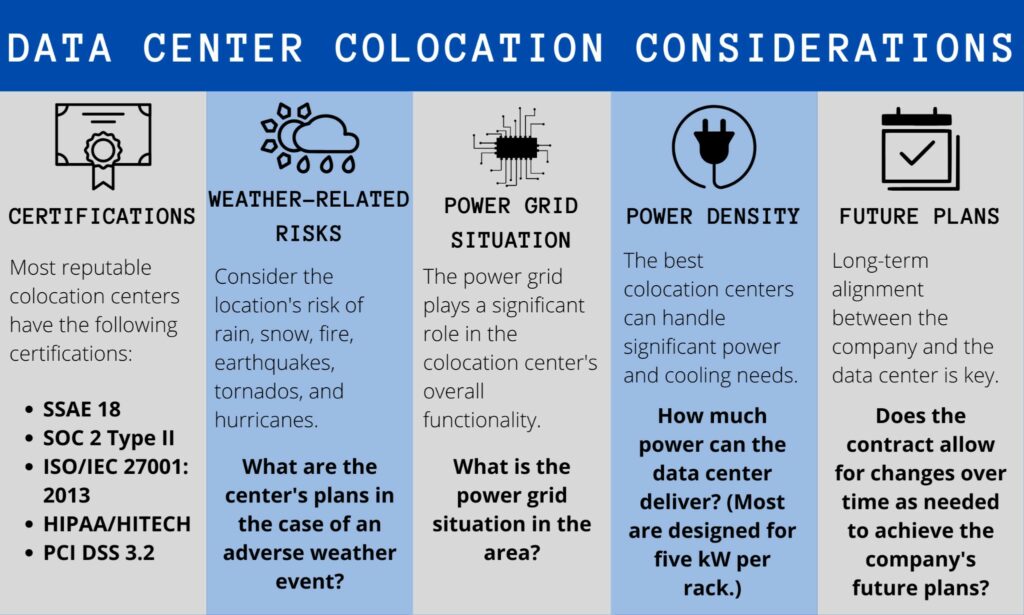
1. What are the provider’s certifications? Colocation centers are generally very transparent about their certifications, so it’s a red flag if a facility isn’t open about them. Most reputable buildings have the following certifications:
- SSAE 18, the Statement on Standards for Attestation Engagements 18: This is the main auditing standard for service organizations, and it regulates the way companies conduct business and report on compliance controls. It assures customers that companies are being forthright in their actions.
- SOC 2 Type II, the System and Organization Controls Type II: This is an audit focused on information security, particularly for cloud storage. It evaluates proficiency in security, privacy, confidentiality, availability, and processing integrity. Type II audits are done by an independent third party and provide full transparency into how well the facility acts in accordance with data handling standards.
- ISO/IEC 27001: 2013, The International Organization for Standardization/International Electrotechnical Commission 27001: 2013: This is an Information Security Standard that tests a facility’s overall effectiveness against international standards as far as its Information Security Management System. A facility with an ISO/IEC 27001: 2013 Certificate of Registration ensures a secure environment for business and brands’ technology and application deployments.
- HIPAA/HITECH, the Health Insurance Portability and Accountability Act/Health Information Technology for Economic and Clinical Health Act: This sets national standards for the security and privacy of electronically protected health information, and it imposes some of the strictest compliance standards in existence. Any companies that have contact with the healthcare industry must ensure that their colocation center is HIPAA/HITECH-compliant.
- PCI DSS 3.2, the Payment Card Industry Data Security Standard 3.2: This is a worldwide security standard that protects personal financial data from electronically processed credit card payments. It’s vital for combating information theft and credit card fraud and is essential for any company that stores financial data or processes credit card payments. Complying with the PCI DSS 3.2 means a data center can ensure that all financial information is protected according to the law.
2. What weather-related risks affect the data center? Consider whether the facility is located in an area where there is an increased possibility of events such as hurricanes, tornados, earthquakes, snow, rain, and fire. If the data center is located in such a location, what are its plans and procedures should an adverse weather event take place? It’s often a better strategy to choose a colocation center that does not experience these weather-related risks.
3. What is the power grid situation in the area? Consider the way 2021’s unexpected storms recently impacted Texas. The power grid plays a huge role in the overall functionality of a colocation data center.
4. What is the facility’s power density? It’s important to understand how much power the data center can deliver. Most data centers are designed for about five kW per rack, and many of today’s technologies require significant power and cooling. A data center with limitations on power and cooling is likely not a good fit for the company.
5. What are the data center’s future plans? For successful colocation, it’s necessary to have long-term alignment between the data center and the company. Ensure that the contract allows for changes over time relating to the company’s future plans.
Now that we’ve covered some of the services you may wish to consider, let’s get back to the other telecommunications needs you’ll want to think over.
The Company’s Budget

Before sending out RFPs and entering into negotiations, your company must establish a telecom budget. The procurement team must know its bottom line and how much it can reasonably spend on telecommunications.
To prepare a telecom budget, auditing the organization’s telecom infrastructure is a step that you shouldn’t skip. An audit can identify incorrect contract rates, misapplied billing, unused services, and more, enabling the company to improve its productivity while eliminating unnecessary costs.
Continuous audits are beneficial, but a minimum of a yearly audit is highly recommended. Market research can also help procurement teams set a reasonable budget for telecom.
TEM (Telecom Expense Management) services are extremely valuable when it comes to developing a telecom budget as well. If you’re interested in TEM services, contact Technology Procurement Group by filling out the form at the bottom of the page.
Should the Procurement Team Focus Primarily on Cost Savings?
Over the years, IT sourcing has evolved quite a bit. In the past, it mainly emphasized the standardization of the purchasing process and aimed to find as much cost savings as possible. These objectives are still relevant today, but now another key goal is revenue generation.
Because of this, procuring telecom products and services isn’t just about cutting spending; it’s also about spending more wisely.
Many organizations are moving from a cost-savings model to a business case model. As a result, sourcing has become more aligned with each investment’s anticipated outcome.
Focusing only on cost savings isn’t always the best strategy. Maintaining a more holistic approach that also incorporates spending wisely to generate revenue is a better route for modern businesses.
Importance of Customer Service and Support
- Thinking about the company’s past and current experiences with customer service and support, how much of a priority is it?
- Does the business wish to look for a vendor that emphasizes fast and effective support for its customers?
- How important is customer service and support in relation to the organization’s other priorities?
Current and Future Business Objectives
It is vital for your business to identify both its short-term and long-term goals as they can impact your choice of vendor. Engaging in technology roadmapping by researching anticipated technology changes over the next 24 to 36 months is crucial for identifying future business objectives. Enterprises should look at these anticipated technology changes and determine how to prepare for and leverage them.
Companies can familiarize themselves with upcoming technology changes and advancements by meeting with various vendors before writing the RFP. Another viable option is to meet with industry experts and consultants to gain additional insight.
Effective technology roadmaps should include an outlined digital transformation strategy that supports the achievement of the business’s short-term and long-term goals.
Ideally, this roadmap should be designed to interface with other internal systems and cloud SaaS (Software as a Service) services. These include Office 365, VMware, Windows Azure, Google, Dropbox, and Salesforce Amazon Web Services (AWS), among others.
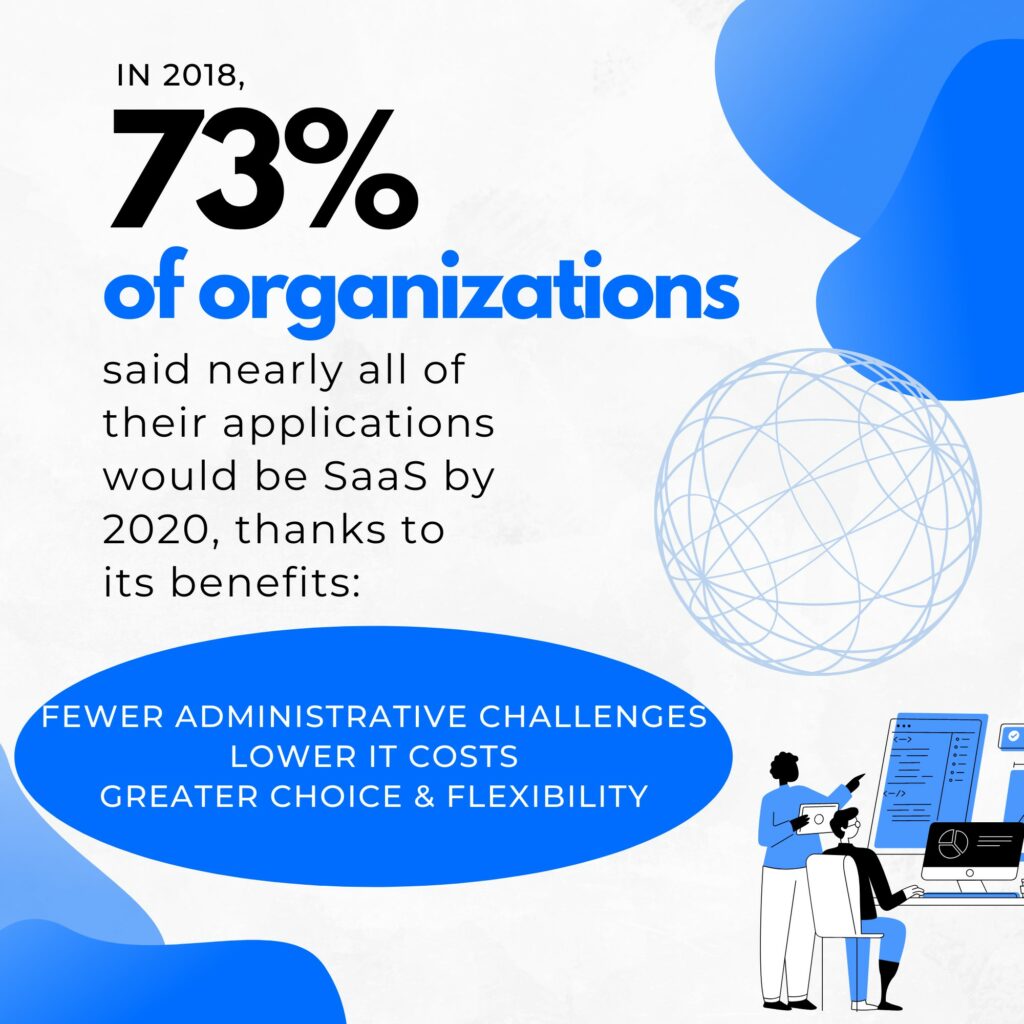
According to Citrix, in 2018, 73% of organizations said that nearly all of their applications would be SaaS by 2020 due to the obvious benefits of Software as a Service. These benefits include fewer administrative challenges, lower IT costs, and greater choice and flexibility.
Current Pain Points

To fully understand your organization’s telecom needs, it’s crucial to identify the pain points that must be considered. Discussing these pain points in the RFP gives vendors a chance to offer solutions and explain product and service capabilities that can address them.
Need for Scalability
Does your company anticipate significant growth within the next few years? If so, it will need a telecom vendor that can accommodate that growth. It’s imperative for your business to receive the same level of service from its telecom provider regardless of its size.
RFP Projects
When identifying the business’s telecom needs, it’s wise to consider whether it would be better to divide the RFP into separate projects. For example, your organization may send RFPs to separate vendors for different needs. It may separate its telecom needs based on geography; maybe your company wishes to select different regional telecom carriers for offices in varying locations.
Or perhaps a better strategy would be to separate the project by technology type. One example is a company that bids its voice services separately from its data network.
Several benefits come with separating the RFP into multiple projects. Having multiple smaller, specialized projects can push vendors to focus and refine their bids. It can also appeal to specialized vendors who are ideal for certain areas.
These types of vendors may not bid at all if they believe they can’t win the entire RFP, or if they think that the company won’t select them since they can’t do it all in the way that large vendors can.
Streamline Your Procurement Process with Technology Procurement Group

Here at Technology Procurement Group, we specialize in helping organizations make the most of their telecom and IT procurement processes.
Not only do we offer telecom procurement strategy consulting and IT procurement services, but we also provide telecom expense management services, wireless expense management services, RFP management, wireless expense reduction, and telecom contract negotiation.
Ready to work with us, or interested in getting more information? Call us at 1-888-449-1580, email us at info@TPG-llc.com, or fill out the simple form on our Contact Us page. We look forward to sharing our expertise with you!




